The median time from referral to first home health visit exceeds 69 hours in 2026
More than 13 of those hours are lost inside the intake process alone. Referral conversion rates have dropped from 77 percent in 2018 to 64 percent in 2025. 39 percent of home health providers turned away cases they could not process fast enough to staff.
Generic patient scheduling software models intake as a data-entry task. Your intake workflow is a conversion funnel. Every referral that stalls is a patient your competitor admits instead, a physician relationship at risk, and a census shortfall in your next PDGM episode period. Meanwhile, a five-state Medicaid footprint can require 7 to 10 distinct EVV integrations, each with its own schema, enforcement threshold, and compliance deadline. The HIPAA Security Rule NPRM is proposing to turn previously optional encryption and MFA controls into hard requirements.
This guide covers what those three forces mean for your platform architecture, what custom patient scheduling software actually costs to build at the module level, and where the build vs. buy breakeven sits against your specific patient ADC and state footprint.
Most home health agencies evaluating patient scheduling software are looking at the same set of platforms: WellSky, Axxess, Homecare Homebase, AxisCare, Alora, and KanTime. For a single-state Medicare-certified agency with a census below 200 patients ADC and standard clinical workflows, one of these platforms is almost certainly the right answer. This guide is not arguing otherwise.
The question this guide addresses is narrower and more specific: at what point does the architecture of a generic licensed platform become the operational bottleneck rather than the cost savings?
Three conditions signal that threshold, First, your agency operates across multiple states with different Medicaid rules, different EVV aggregator requirements, and different payer contracts that no generic patient scheduling software models correctly. Second, your clinical workflows or authorization logic are specific enough to your contracts that coordinators have built spreadsheet workarounds because the platform cannot accommodate the rules. Third, you need to own your patient data for longitudinal analytics, health system EHR integration, or value-based care contracts that require direct data feeds.
If none of those three conditions apply, the licensed SaaS options above are worth evaluating on price and feature fit. If one or more apply, the rest of this guide covers what a purpose-built custom patient scheduling software costs to build, what it requires architecturally, and where the breakeven sits against your specific scale.
More than 70 percent of home health referrals still arrive via fax. Each one requires a coordinator to manually extract demographics, verify insurance, check authorization requirements, confirm geographic coverage, and match against available clinician capacity before a single visit is ever scheduled. Industry data consistently puts this at 25 to 30 minutes per referral for agencies using off-the-shelf intake workflows.
The time cost is the symptom. The structural problem is that generic platforms model intake as a data-entry task. Your intake workflow is a conversion funnel and every stalled referral is a patient who may be admitted by a competing agency, a physician relationship at risk, or a census shortfall in your next PDGM episode period.
Custom intake architecture treats the referral as a structured event with a conversion timeline. Authorization logic, payer rules, and geographic matching run at intake time.
A custom-built intake engine maps your specific authorization logic for each payer, your coverage rules by geography and service line, and your clinician availability model directly into the referral workflow. The result is a coordinator who sees at the moment the referral arrives whether can be admitted, which clinician is available, and what the authorization pathway looks like. It is an architectural decision about where business logic lives.
A purpose-built platform for home health must handle what generic patient scheduling software cannot. The feature set maps directly to the operational failure points that cause referral leakage, compliance gaps, and billing denials.
Referral intake and capture: Structured eFax-to-data extraction, portal intake, and phone intake channels feeding a single referral queue. Authorization logic, payer rules, and geographic coverage checks running at intake time and not after manual data entry is complete. Coordinators should see admittability, clinician availability, and the authorization pathway the moment a referral is created.
Insurance eligibility and authorization management: Real-time eligibility verification at intake, payer-specific authorization rules configured to your actual contract schedule. Medicare Advantage plan rules vary by contract and a platform that cannot model that variation forces coordinators into spreadsheet workarounds.
OASIS-E2 data collection and validation: Updates effective April 1, 2026 introduced new data requirements for patient sex fields, transportation tracking, and expanded hearing, vision, and language assessments at resumption of care. Any custom patient intake system built or upgraded in 2026 must account for these at the data model level.
Caregiver-patient matching: Skill-based, geography-based, availability-based, and continuity-preference matching visible to intake coordinators in real time, running against live clinician schedules rather than a static availability flag.
EVV integration: Visit verification data flowing directly from the clinician mobile app to the appropriate state aggregator without a manual reconciliation layer. Multi-aggregator support is not optional for multi-state operations.
Role-based access control and audit logging: Five distinct roles minimum with attribute-based context controls limiting PHI access to active visit windows. Immutable audit log to write-once storage with six-year retention.
Billing integration: 837/835 transaction support, Medicaid multi-state payer rules, PDGM grouper logic, and real-time claim scrubbing before submission. Billing errors that originate in custom patient intake are the most expensive category of rework in home health operations.
AI-powered triage and intake automation: Production deployments exist now and are covered in the AI section below.
OASIS-E2 updates took effect April 1, 2026. Three data requirement changes affect custom patient intake architecture directly.
Patient sex data fields: OASIS-E2 now requires collection of both sex assigned at birth and gender identity as separate discrete fields. Any intake data model built before April 2026 using a single gender or sex field requires a schema change. The distinction matters for data migration: historical records mapped to a single field cannot be automatically split into two discrete clinical data points.
Transportation item (M1033): The OASIS-E2 transportation item now tracks transportation as a social determinant of health at resumption of care in addition to start of care. Intake and documentation software that does not surface this item at resumption-of-care assessments will generate incomplete OASIS submissions and create downstream billing risk.
Hearing, vision, and language assessments at resumption of care: These assessments, previously required only at start of care and discharge, are now required at resumption of care. Documentation workflows that do not enforce this requirement at resumption triggers will produce noncompliant OASIS records.
The practical consequence for platform builds: any custom patient intake and scheduling system being scoped in 2026 must model OASIS-E2 compliance at the data schema level from Day 1. Retrofitting a data model that did not account for these requirements costs significantly more than building them in at design time and the compliance exposure during the retrofit window creates direct billing denial risk.
The 21st Century Cures Act Section 12006(a) required EVV for all Medicaid-funded home health services by January 1, 2023. Federal mandate established the floor. What it did not establish is architectural coherence. Forty-three states and DC now operate live EVV systems across eight distinct aggregator platforms each with its own data schema, authentication model, submission protocol, and compliance threshold.
Hard enforcement transitions are accelerating. Michigan required HHAeXchange integration with an 85 percent quarterly compliance threshold effective January 1, 2026. North Carolina's managed care hard launch took effect October 1, 2025 and NC runs three aggregators simultaneously: Sandata for Medicaid Direct, HHAeXchange for most MCOs, and CareBridge for select MCOs. Missouri went to hard claims denial for provider types 26 and 28 on April 1, 2026. Texas continues its hard enforcement posture with proposed rule updates published April 2026.
2026 EVV enforcement snapshot by state:
A five-state portfolio covering Texas, North Carolina, Florida, Pennsylvania, and Illinois requires between seven and ten distinct integration endpoints because NC runs three aggregators, Pennsylvania splits across Sandata and HHAeXchange by payer type, and Florida's FFS and MCO layers use different platforms. Each aggregator carries its own visit-key generation rules, flat-file versus JSON schema variants, and state-specific compliance thresholds.
Major licensed platforms bill EVV integrations as add-ons: per-aggregator fees, per-state licensing, and delayed support for new state specs. When Missouri moved to hard enforcement in April 2026, agencies on platforms that lagged the spec update had no path to compliance without manual workarounds which directly triggered denied claims.
The compounding operational and financial cost in integration maintenance, manual reconciliation, delayed compliance, and denied-claim recovery that health systems pay when their EVV architecture was designed for one state's rules and stretched across many is real and measurable. Each new state hard-enforcement transition multiplies it.
The December HIPAA Security Rule NPRM (89 FR 104520) proposes the most significant overhaul of the Security Rule since 2013. The central change eliminates the addressable versus required distinction across implementation specifications. If finalized, the following become outright required: AES-256 encryption of ePHI at rest and in transit, multi-factor authentication, annual penetration testing, semi-annual vulnerability scanning, asset inventory, and network mapping.
As of April 2026, the rule is proposed but not final, a regulatory freeze has slowed the timeline. The prudent posture for a new platform build is to architect to the NPRM today. Retrofitting a deployed mobile platform to add proper offline-sync encryption or role-based access control costs 3 to 5 times what it costs to build them in from the start.
The unique HIPAA exposure in home health is not the clinic server. It is the clinician's phone in the patient's living room. Hundreds of residential sites, BYOD devices, unsecured home WiFi, and intermittent rural connectivity create a PHI exposure surface that no amount of portal encryption addresses if the offline sync layer is not built correctly.
Offline sync security: PHI persists only in NSFileProtectionComplete containers on iOS, keyed to device passcode and Secure Enclave UID. On Android, Jetpack Security EncryptedFile with keys bound to Keystore StrongBox. Auth tokens stored with biometric binding that invalidates on re-enrollment. Access tokens expire in 15 minutes; refresh tokens rotate on every use per RFC 6749. After 24 hours offline, step-up biometric plus PIN reauth is required before any PHI is accessible. On reconnect, prior refresh tokens are revoked.
Push notifications and the APNs/FCM BAA gap: Apple and Google do not sign a BAA for their push notification services. PHI cannot appear in notification payloads under any circumstances. The compliant pattern is generic-alert plus pull-on-unlock the server sends a content-available payload with no PHI, the app wakes and authenticates to your server, PHI is fetched into the encrypted local store, and display occurs only after biometric or PIN unlock. Any platform surfacing patient names or appointment details in push previews is out of compliance with 164.502(b).
AI-powered intake automation is in production at home health agencies today, and the performance gap between agentic intake systems and manual coordinator workflows is widening.
What production AI intake deployments are handling now: structured eFax-to-data extraction using document AI that pulls demographics, diagnosis codes, payer information, and authorization data from unstructured fax content with accuracy rates above 95 percent on well-formatted referral documents; eligibility verification running automatically against payer APIs at the moment intake data is extracted, before any coordinator review; authorization logic evaluation against configured payer rules, surfacing the authorization pathway and any missing documentation requirements at intake time rather than after the coordinator completes data entry.
What agentic AI intake means operationally: an agentic intake system does not assist the coordinator, it completes the structured portion of intake and presents the coordinator with a decision. The coordinator reviews admittability, available clinician matches, and the authorization status rather than constructing them from raw fax content. For high-volume referral operations, this shifts coordinator capacity from data entry to clinical judgment and exception handling.
HIPAA compliance requirements specific to AI intake systems: AI models processing PHI are covered entities or business associates under HIPAA and require a BAA with the AI service provider. Model inputs and outputs that contain PHI must be encrypted in transit and at rest under the same AES-256 requirements as any other ePHI. Audit logging of AI decisions affecting PHI, what data the model processed, what output it produced, what action the system took is required under 164.312(b). AI models trained on historical PHI require a formal privacy analysis under 164.514(b) before training data is used.
Agentic AI in home health intake is a current architectural decision about whether your custom patient intake platform is built to support it from Day 1 or retrofitted after go-live at significantly higher cost and compliance risk.
Is your custom patient intake and scheduling architecture ready for multi-state EVV enforcement and the HIPAA NPRM?
Ideas2IT runs a no-cost 90-minute Architecture Decision Session for health system CTOs and VP Engineering. The output is three things: a current-state EVV aggregator coverage map against your state footprint, a module-level scoping estimate calibrated to your specific payer mix and compliance requirements, and a HIPAA mobile architecture gap assessment against the NPRM's proposed requirements. Engineers only.
Request the Architecture Session
Generic platforms make four architectural compromises that health systems feel operationally within 12 months of go-live. A purpose-built engagement resolves each at design time.
Ideas2IT builds custom home health intake and scheduling platforms as a Forward Deployed Engineering engagement. The FDE model means engineers embed inside your existing engineering organization from Day 0, your stack, your standups, your OKRs. It is an embedded team operating inside your environment with your product goals, backed by a proprietary platform suite that compresses delivery timelines structurally.
Ideas2IT is an AWS GenAI Specialist Partner with 800 engineers, SOC 2 Type II and ISO 27001 certifications, and HIPAA compliance.
Proprietary accelerators reduce delivery timeline on every home health build:
Claims data and patient data from multiple source systems is unified 80 percent faster than manual data engineering, normalizing the inputs the platform needs before development begins, not after the first migration attempt fails. (MigratiX)
The integration development cycle the critical path on every custom patient intake project is compressed from the first week. (Explayn.ai)
70 percent of test cases are auto-generated, producing compliance-grade regression coverage across intake scenarios, EVV workflows, and HIPAA control edge cases without dedicated QA headcount. (Qadence)
Live operational visibility into referral conversion rate, EVV reconciliation lag, authorization exception rate, and PDGM episode performance the metrics that show whether the platform is compounding or stalling. (DataStoryHub)
The $50K to $500K ranges that dominate web content are not useful for a board-level capital decision. The estimates below are module-level, triangulated across multiple healthcare development cost benchmarks and reconciled with Accelerance 2025 Global Outsourcing Rates. These are mid-case estimates on a hybrid team at $90/hr blended. US onshore at $150/hr is shown for comparison.
Three build scenarios:
MVP: intake, scheduling, mobile, one EVV aggregator, basic billing, HIPAA infrastructure: 4,000 to 5,500 hours, $360K to $495K hybrid, 6 to 9 months, approximately 8 FTE.
Standard full platform: full module set, three to five EVV aggregators, Medicare PDGM plus three to five Medicaid states, OASIS-E2, portal, analytics: 10,000 to 13,000 hours, $900K to $1.17M hybrid or $1.5M to $1.95M onshore, 12 to 18 months, 12 to 14 FTE.
Enterprise multi-tenant: 20-plus state Medicaid, full aggregator matrix, Epic/Cerner FHIR integration, HITRUST r2, 24/7 operations: 18,000 to 25,000 hours plus $150K to $300K compliance overhead, 18 to 24-plus months.
Annual maintenance runs 20 to 30 percent of initial build for healthcare platforms higher than the general software benchmark because of continuous CMS regulatory changes, state EVV spec updates on an approximately 12-month cycle, and mobile OS patching requirements under the NPRM's proposed semi-annual scanning mandate. A $1.5M standard build generates approximately $375K per year in maintenance and $1.88M in cumulative five-year maintenance.
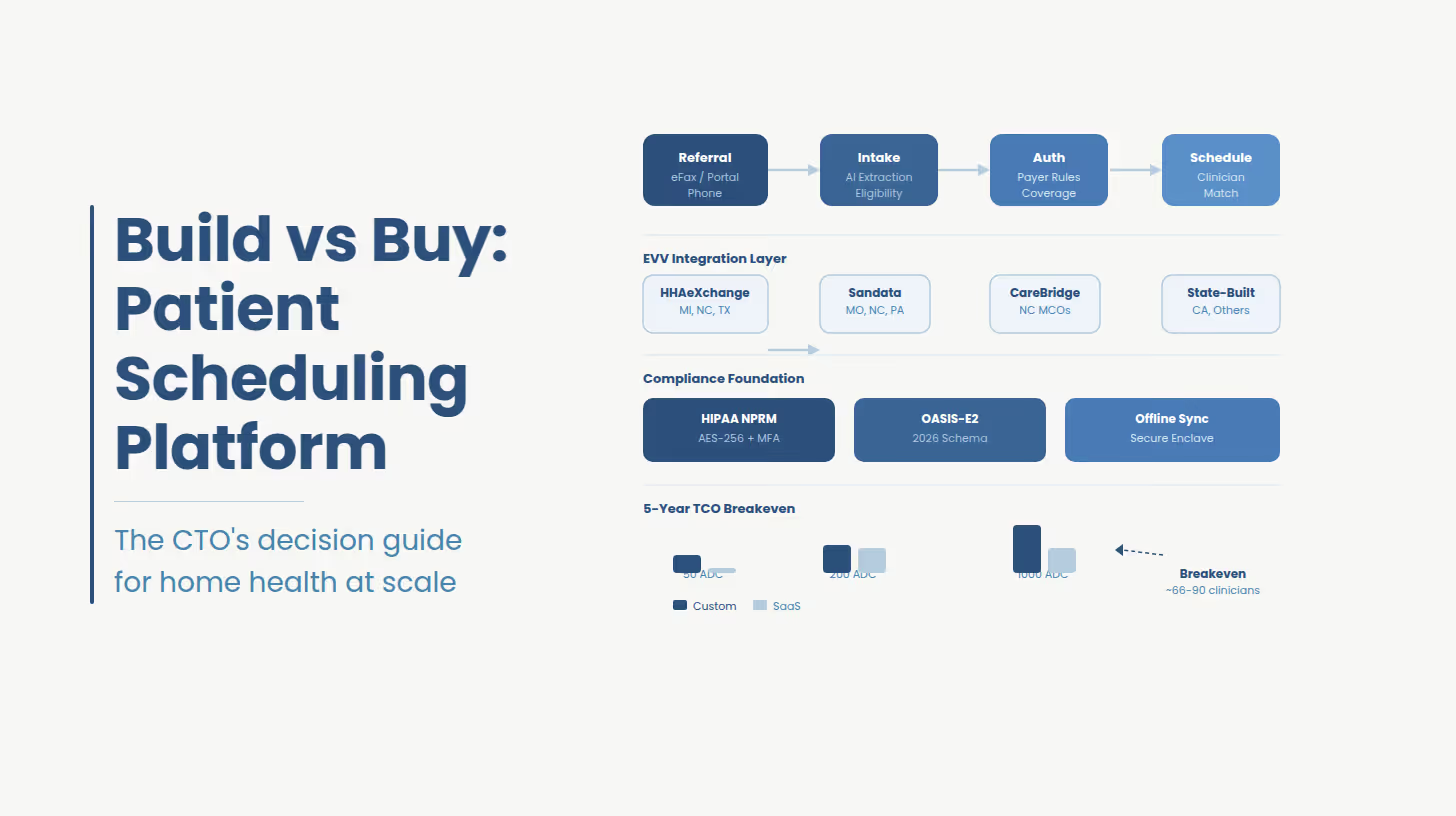
Build vs. Buy Patient Scheduling Software: Five-Year TCO at Three Agency Scales
Vendor per-seat rates used: WellSky approximately $800/user/month, Axxess approximately $899/user/month per SelectHub and G2 estimates; neither publishes list pricing. HCHB enterprise rates are not publicly disclosed; the figure above likely understates large-system contracts. Treat these as directional.
Build vs. buy breakeven sits at approximately 66 to 90 clinicians, approximately 265 to 340 patient ADC on a five-year TCO basis against WellSky or Axxess. Below this threshold, licensed SaaS wins on cost. Above it, every additional clinician inverts the math. Against HCHB or KanTime, custom rarely wins on pure TCO below approximately 1,000 patient ADC the strategic case above that threshold is multi-state aggregator complexity, data ownership, and the inability to move faster than your vendor's compliance roadmap.
A post-acute care network managing more than 1,300 community-based care organizations across 35 states had built its intake and scheduling workflow on top of a legacy clinical documentation system not designed for multi-payer, multi-state Medicaid billing. Every new state entered required a separate manual integration project. EVV data flowed through a middleware layer that introduced a 48-hour reconciliation lag denied claims were not identified until two billing cycles had passed.
Engagement outcomes, post-acute care network, 35-state footprint:
The middleware EVV layer was replaced with a unified aggregator adapter architecture supporting HHAeXchange, Sandata, and AuthentiCare under a single API contract. EVV reconciliation lag reduced from 48 hours to same-day within 90 days of go-live.
The intake workflow was rebuilt around structured eFax-to-data extraction, eliminating 25 to 30 minutes of manual referral entry per admission.
Authorization logic and payer rules were embedded directly into the intake funnel coordinators see admittability, clinician availability, and authorization pathway at the moment the referral is created.
HIPAA infrastructure was scoped to HITRUST i1 from the start; documentation was sufficient for health system vendor risk review within six months of platform launch.
Ideas2IT FDEs embedded inside the client's existing engineering organization same OKRs, same standups, same stack.
Is your custom patient intake and scheduling architecture ready for multi-state EVV enforcement and the HIPAA NPRM
Ideas2IT runs a no-cost 90-minute Architecture Decision Session for health system CTOs and VP Engineering. The output is three things: a current-state EVV aggregator coverage map against your state footprint, a module-level scoping estimate calibrated to your specific payer mix and compliance requirements, and a HIPAA mobile architecture gap assessment against the NPRM's proposed requirements. Engineers only. No pitch deck.
Request the $0 Scoping Session
[1] ONC / HealthIT.gov — "'Six things to know about health IT adoption and provider communication' — fax use in referral workflows" https://www.healthit.gov/buzz-blog/health-it/six-things-to-know-about-health-it-adoption-and-provider-communication
[2] Homecare Homebase / industry ops data — "Coordinator referral entry time 25–30 min — cited across multiple vendor operational benchmarks and confirmed in G2/Capterra review patterns" https://www.hchb.com (vendor documentation; see also Capterra verified reviews)
[3] CMS — Medicaid.gov — "Electronic Visit Verification — 21st Century Cures Act Section 12006(a) mandate overview" https://www.medicaid.gov/medicaid/home-community-based-services/home-community-based-services-authorities/home-health-services/electronic-visit-verification/index.html
[4] Michigan DHHS — Bulletin MMP 26-10 — "EVV for MI Choice Waiver, Adult Home Help, and Medicaid State Plan HHCS — HHAeXchange mandate effective Jan 1, 2026, 85% quarterly threshold" https://www.michigan.gov/mdhhs/-/media/Project/Websites/mdhhs/Assistance-Programs/Medicaid-BPHASA/2026-Bulletins/Final-Bulletin-MMP-26-10-EVV.pdf
[5] NC Medicaid — ncdhhs.gov — "Managed Care Electronic Visit Verification Home Health Implementation Hard Launch Effective Oct. 1, 2025" https://medicaid.ncdhhs.gov/blog/2025/06/03/managed-care-electronic-visit-verification-home-health-implementation-hard-launch-effective-oct-1
[6] Missouri DSS — mydss.mo.gov — "EVV Claims Validation — Non-Compliant Claims Will Deny Beginning April 1, 2026" https://mydss.mo.gov/mhd/hot-tips/evv-claims-validation-non-compliant-claims-will-deny-beginning-april-1-2026
[7] Texas TMHP — "Public Comment Period for Proposed EVV Rule Updates — April 9, 2026" https://www.tmhp.com/news/2026-04-09-public-comment-period-proposed-evv-rule-updates
[8] Federal Register — 89 FR 104520 — "HIPAA Security Rule to Strengthen the Cybersecurity of Electronic Protected Health Information — NPRM January 6, 2025" https://www.federalregister.gov/documents/2025/01/06/2024-29976/hipaa-security-rule-to-strengthen-the-cybersecurity-of-electronic-protected-health-information
[9] HHS.gov — "HIPAA Security Rule NPRM Factsheet — proposed elimination of addressable/required distinction" https://www.hhs.gov/hipaa/for-professionals/security/hipaa-security-rule-nprm/factsheet/index.html
[10] HHS.gov — OCR Resolution Agreement — "Lifespan ACE Pays $1,040,000 to OCR to Settle Unencrypted Stolen Laptop Breach — July 2020" https://www.hhs.gov/about/news/2020/07/27/lifespan-pays-1040000-ocr-settle-unencrypted-stolen-laptop-breach.html
[11] NIST — csrc.nist.gov — "NIST SP 800-124 Rev. 2: Guidelines for Managing the Security of Mobile Devices in the Enterprise" https://csrc.nist.gov/pubs/sp/800/124/r2/final
[12] HHS.gov — OCR Resolution Agreement — "Children's Hospital Colorado Pays $548,000 — MFA disabled on physician account enabling phishing — December 2024" https://www.hhs.gov/hipaa/for-professionals/compliance-enforcement/agreements/childrens-hospital-colorado/index.html
[13] HHS.gov — OCR Civil Money Penalty — "Gulf Coast Pain Consultants $1,190,000 CMP — access termination and activity review failures — December 3, 2024" https://www.hhs.gov/hipaa/for-professionals/compliance-enforcement/agreements/gulf-coast-pain-consultants/index.html
[14] IBM Security — "Cost of a Data Breach Report 2024 — healthcare sector average $7.42M–$9.77M" https://www.ibm.com/reports/data-breach
[15] Ideas2IT Technologies — LegacyLeap — "LegacyLeap agentic application modernization platform — replaces 6–8 weeks manual discovery with 1 week automated; 50–70% faster delivery" https://www.legacyleap.ai
[16] NIST — csrc.nist.gov — "NIST SP 800-66 Rev. 2: Implementing the HIPAA Security Rule — A Cybersecurity Resource Guide (February 2024)" https://csrc.nist.gov/pubs/sp/800/66/r2/final
[17] U.S. Congress — Public Law 116-321 — "HR 7898 — HITECH Recognized Security Practices amendment, signed January 5, 2021" https://www.congress.gov/116/plaws/publ321/PLAW-116publ321.pdf
[18] AxisCare — "2025 State of Home Care Industry Survey — EVV as significant concern, tech spend as % of revenue" https://www.axiscare.com/blog/state-of-home-care-report/
[19] HHAeXchange — "Michigan EVV Information Center — aggregator mandate documentation" https://www.hhaexchange.com/info-hub/michigan-information-center
[20] Gartner — "Software Engineering 2030: The Impact of AI — developer demand projected +57% by 2030; 16% or fewer engineering leaders believe their architecture is AI-ready" Internal PDF supplied by client — also available at gartner.com/en/information-technology

